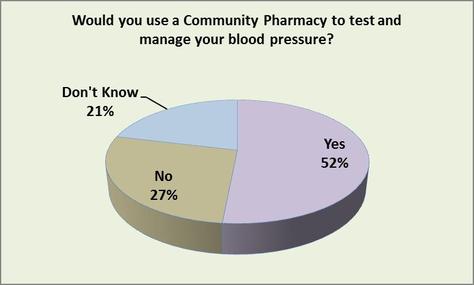
Mini poll shows that over 50% of respondents would use a Community Pharmacy to test and manage their blood pressure.
In a recent mini poll undertaken by Direct Data Analysis, 52% of respondents stated that they would use a Community Pharmacy to test and manage their blood pressure.
In the poll, 27% of respondents stated they wound not use a Community Pharmacy for the service, whilst 21% did not know if they would use a Community Pharmacy to test and manage their blood pressure.
In a recent mini poll undertaken by Direct Data Analysis, 52% of respondents stated that they would use a Community Pharmacy to test and manage their blood pressure.
In the poll, 27% of respondents stated they wound not use a Community Pharmacy for the service, whilst 21% did not know if they would use a Community Pharmacy to test and manage their blood pressure.
Over recent years, Community Pharmacies have been given the opportunity to provide a range of diagnostic and management services to assist patients and save the need for a visit to their GP. However, previous work has shown that a number of people are still unaware that they can use a Community Pharmacy to discuss and manage certain conditions without the need for a visit to their GP. Additionally, previous work has shown that a number of people have concerns over privacy issues around discussing their condition in their local Community Pharmacy.
Whilst every effort has been made to ensure the accuracy of the information supplied herein, Direct Data Analysis Ltd cannot be held responsible for any errors or omissions. Unless otherwise indicated, opinions expressed herein are those of the author of the page and do not necessarily represent the views of the NHS.
www.direct-data-analysis.co.uk
Whilst every effort has been made to ensure the accuracy of the information supplied herein, Direct Data Analysis Ltd cannot be held responsible for any errors or omissions. Unless otherwise indicated, opinions expressed herein are those of the author of the page and do not necessarily represent the views of the NHS.
www.direct-data-analysis.co.uk

 RSS Feed
RSS Feed